Phishing Protection on Mobile
MobilePhishing links really are annoying aren’t they? Between using unicode characters in hostnames and legit looking designs coupled with good English (unlike here at The Serpent), it’s no wonder that this method of hacking an account still reigns supreme.
On most Windows\MacOS and Chromebook machines, you’ll have a fair amount of protection against the usual known malicious crap, but just how fast does this protection typically kick in? Luckily for me, I recently had the chance to test this out!
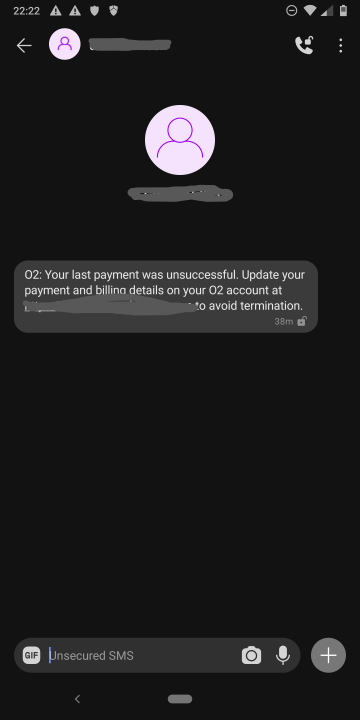
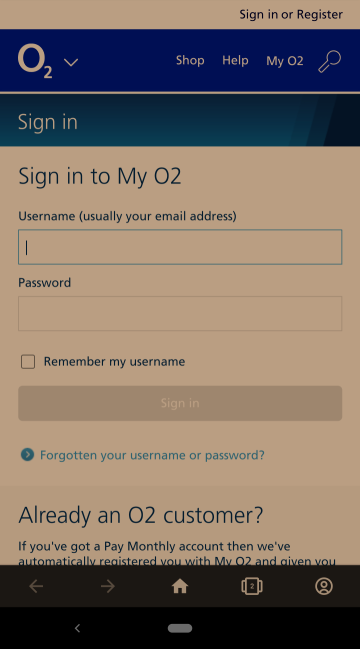
38 minutes ago, I got an SMS from an unknown number. The scam was typical; “Payment rejected, login to update payment details”. I’m assuming my audience already know the usual red flags in these instances, but let’s quickly cover them here:
- From an unknown number, not using a sender ID
- the URL contained in the SMS wasn’t associated with the legitimate company
- I’m not even a customer of theirs
So far so good. We know we’re getting phished.
But what can technology do to actually help me? What if it was my grandmother, or slightly more naive relative? Where’s all this protection that should be kicking in to save me?
Since this happened half an hour ago - it’s a great opportunity to test out the defences. I immediately checked out the baseline standard of computing, Microsoft Edge on a desktop machine - would SmartScreen spring to life and save me?
No, of course not.
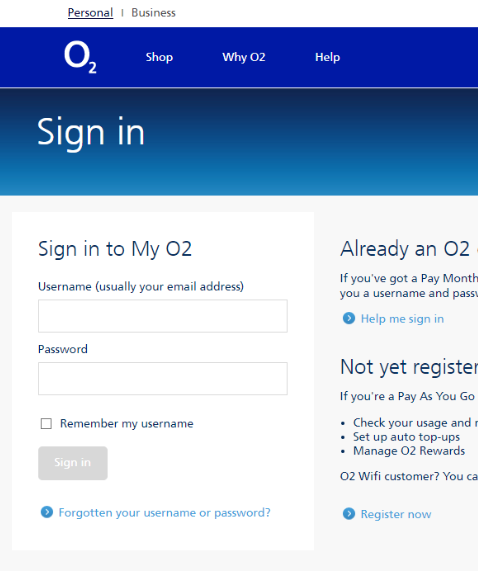
So who actually knows about this site? Let’s load up the other gold standard when it comes to nasty stuff and see who’s alert…
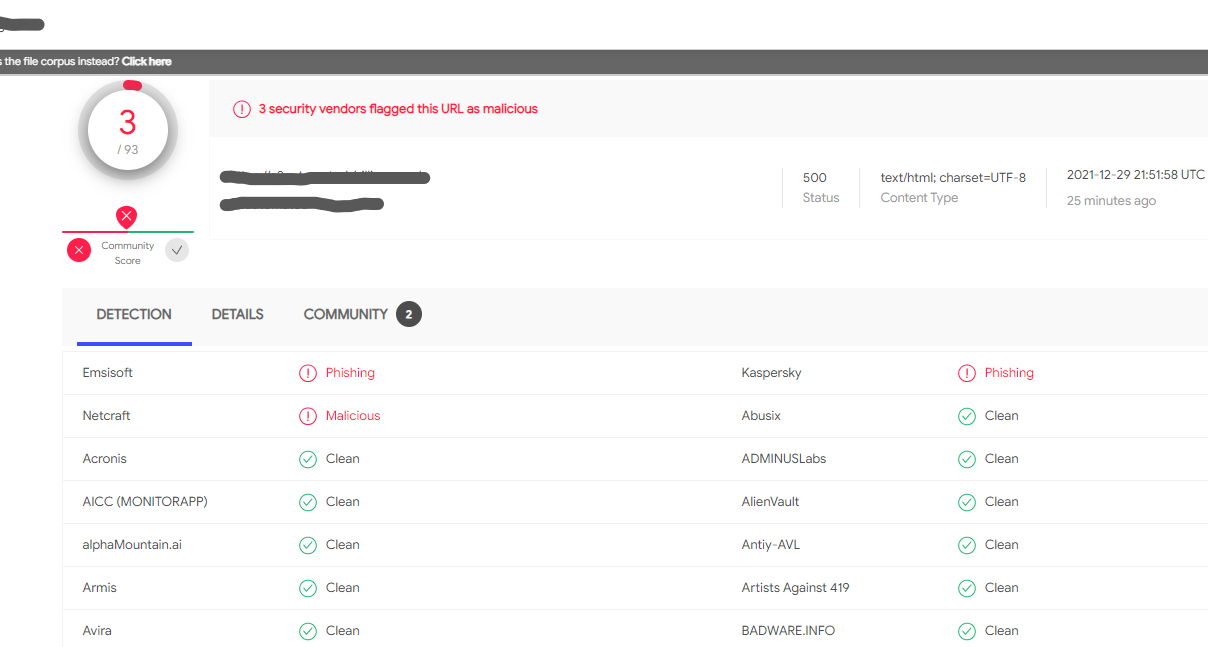
30 minutes in and only three vendors have classified it; Kaspersky, Emsisoft and Netcraft. These guys are fast, but classification doesn’t necessarily mean action, right?
Mobile defences
I’m guessing not many readers are running any kind of mobile defence software. Don’t worry, I won’t judge - not only are there so many to choose from, but they largely all do the same thing, i.e. look for known bad signatures and provide useless features such as Application Locking and Anti-theft. However there are some good ones out there, that should help here.
Forgetting the other 90 vendors who consider this URL safe, I wanted to see if the three above actually transferred their intelligence into the mobile apps and onto my browser. First up - Kaspersky
Kaspersky
These guys get a lot of stick because of their, erm… origin. Being a Russian cybersecurity company is a double-edged sword. On the one hand, you’re well placed to identify a lot of eastern European\Russian malware making its way out of the offices of Fancy Bear and other incredibly skilled and well financed groups; on the other, you’re likely to be accused of working for the Kremlin yourself.
I’ve always been a fan of Kaspersky. They have excellent labs, very skilled people and their technical write ups don’t hold back. I was hoping these guys would have this little SMS phish caught.
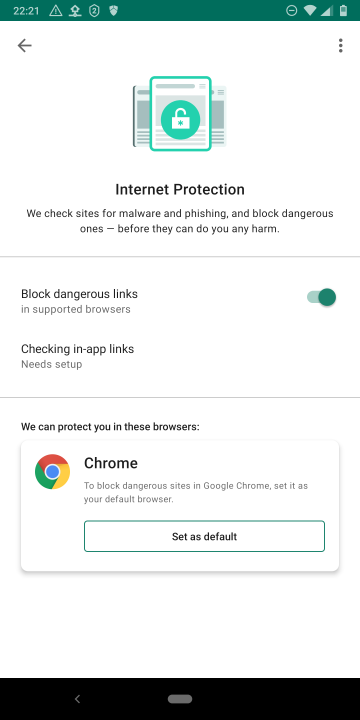
This was a problem for me, since I don’t use Chrome as my default browser. It’s pretty much the only reason I don’t run Kaspersky on Android, otherwise I’d highly recommend them. But I was still curious if they protect Chrome users:
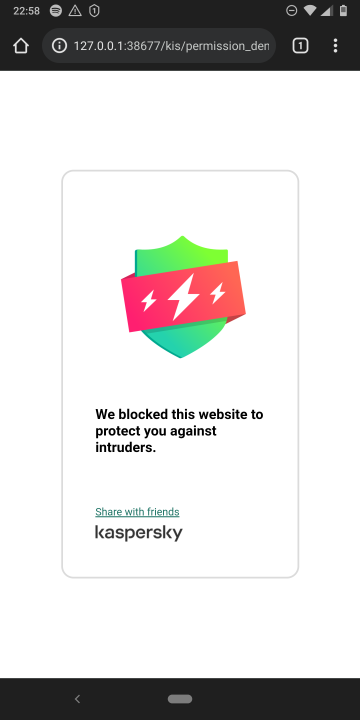
Success! Within an hour of the scam going live, Kaspersky are on it (if you use Chrome). But how did the others do?
Emsisoft
These guys may not be as well known, but they also do some excellent work in the cybersecurity industry. I was hoping they’d have me covered for this test. The good news is that they support my browser:
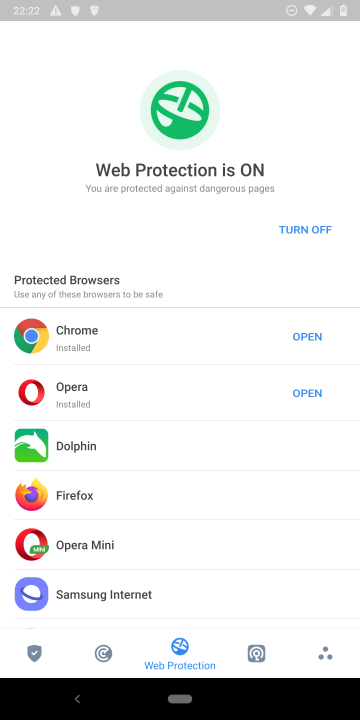
The bad news? Nothing happened…
I’m not sure why Emsisoft didn’t block the site, I can only guess the intelligence hadn’t filtered down to the application yet, or maybe not to my region.
Netcraft
Netcraft are awesome, and old… extremely old. Located in the quaint little town of Bath, UK - they also produce some excellent intelligence for the cyber world. Their Android app is also extremely lightweight, focusing only on phishing protection across a range of browsers, would they protect me in my zero-hour of need?
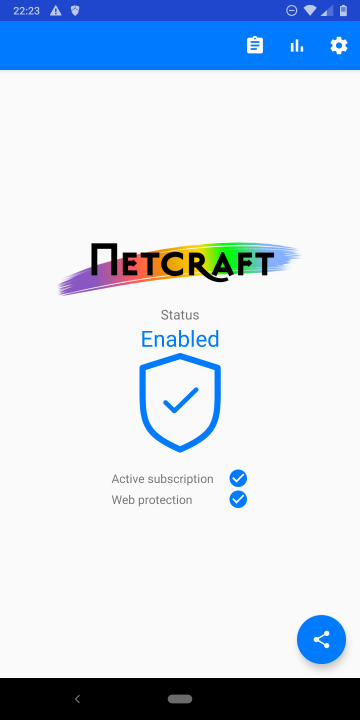
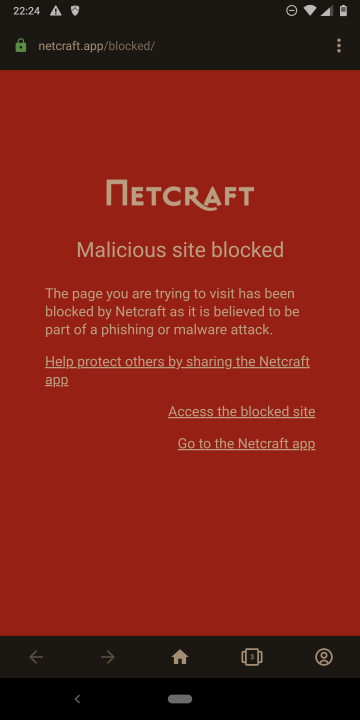
Of course they can. Netcraft are the winners in this little test, not only did they identify the site within an hour of it going live, they also filtered that intelligence out to the community, giving us real-world protection where it’s needed most.
Note that this protection doesn’t come free however. All these apps require subscriptions. Though as we can see, my money goes to Netcraft (and at £1 a month, I think it’s worth it as I get older and the links all start to look the same).
Netcraft is available on Android and iOS, tell your grandmother\naive relatives.
Bonus Chapter
I tend to check out all phishing sites I get, since the creators usually stand them up very quickly and aren’t normally tech savvy. It’s a good opportunity to practice your skills and see what they’ve left open. However to my surprise, the creators of this host took a very different approach to normal and opened all the ports!
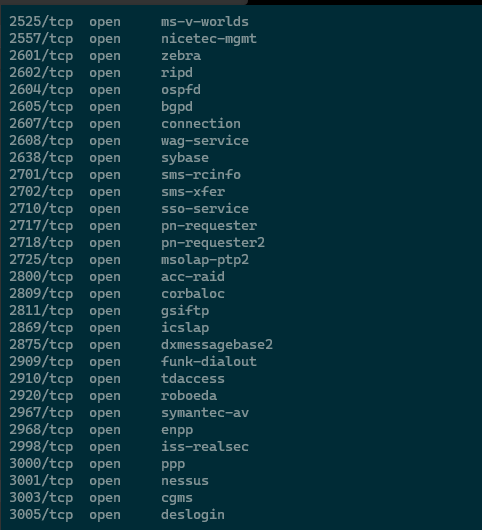
I guess it makes the pentesting take twice as long, eh?